
Avathon/SparkCognition Blogs
Links to various blogs I’ve written during my tenure with Avathon/SparkCognition’s Marketing Team

Achieving World-Class Downstream Operations Performance with AI
Product Brochure I created for the Oil & Gas Practice in support of client business development, trade shows, and other marketing programs.
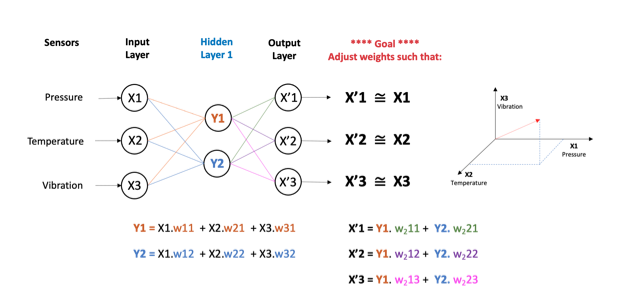
Anomaly Detection Using Normal Behavior Modeling (NBM) for Predictive and Prescriptive Maintenance
Normal behavior modeling (NBM) is an approach to process, system, and equipment management and maintenance that has been enabled by recent advances in the fields of artificial intelligence (AI) and machine learning (ML). This white paper describes the evolutionary forces that have led to this new capability set, its applications (current and prospective), its benefits, and details of how the technology works. In addition to the explanation of NBM’s operation and implementation, several examples are provided that highlight the benefits of this technology.

AI for Renewable Energy eBook
EBook created in support of SparkCognition’s sustainable energy AI programs. This was a very large undertaking that required interviews with at least a dozen SMEs in the firm, followed by several weeks of drafting, researching, and updating prior to release of the final piece for use at trade shows, conferences, etc.

Reimagine Aviation Maintenance with AI
Product brochure that I created for SparkCognition Government Systems highlighting the application of AI/ML-based Normal Behavior Modeling and Predictive Maintenance in the defense industry.
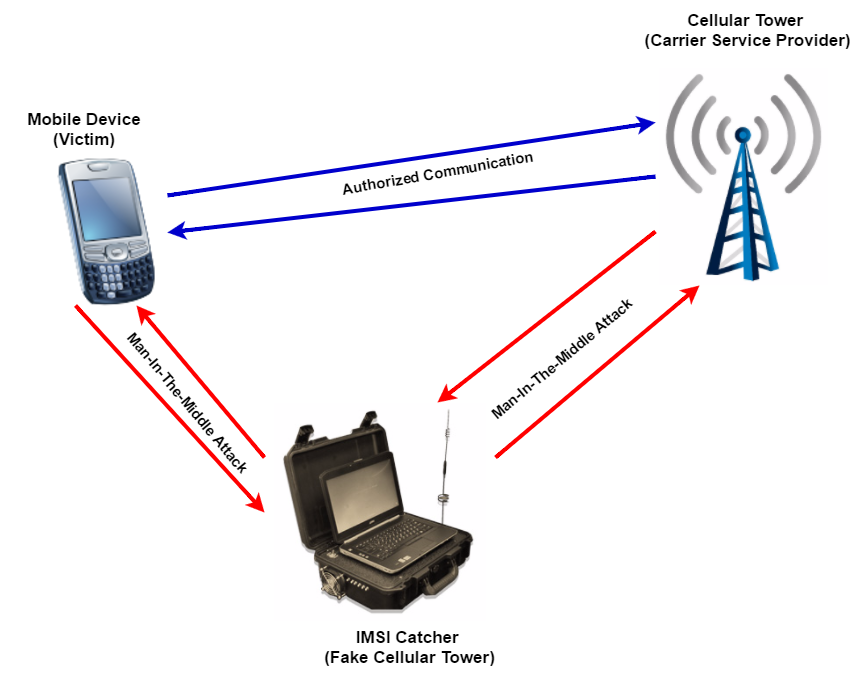
Man in the Middle Attack
The Threat Man-in-the-Middle (MITM) mobile attacks can be accomplished in a wide range of technical ways, but the high level effect is the same in every scenario. An individual manages to insert himself between a call originator and recipient, and manages, as well, to fool each party into believing they are communicating directly with the other desired party, when, in fact, they are each communicating with the attacker.
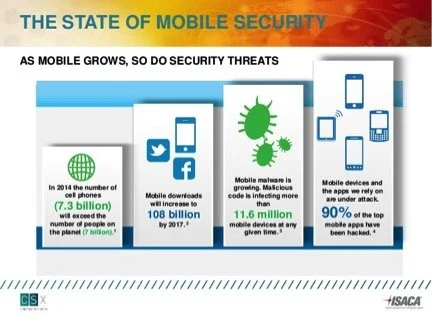
Malware/Spyware Attack
The Threat There exist many types of malware targeting mobile devices. And with the proliferation of mobile phones over the past decade, malware developers have dramatically ramped up their efforts to create and distribute malicious software to the cell phone community. Unsurprisingly perhaps, financial attacks are the single largest category of malware.
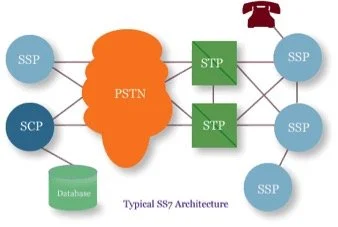
Hacking the CCS7 Network
The Threat The CCS7 network was developed in the mid seventies to control the routing of phone calls using out-of-band signaling. The data packets transmitted on the network control not only the initiation and completion of calls, but also numerous billing functions and the activation of advanced features that are today taken for granted (call forwarding, call waiting, etc.).

Baseband Attack
The Threat The baseband processor in a mobile phone is the system that communicates via radio waves with the cell tower in order to complete cellular calls. Because your mobile phone communicates via cell towers, in order to intercept the radio signal from a cell phone, the hacker must first set up a fake cell tower and convince a nearby phone (the target) to connect to it.